Just as integrity is doing the right thing when no one is watching – paranoid is thinking people are watching when they are not. People always wonder, is Tor an FBI Honeypot?
It is always safer to assume no form of communication is secure. This is true for the spoken word, telephone, and computer transmissions. Just because it is not a honeypot now, it is subject to change in the future. Until then, this article will answer common questions and help you avoid falling victim to a honeypot.
Table of Contents
What is a Honeypot Trap?
If you Google the term honeypot, you will get a range of different topics. This article focuses only on a honey pot in cybersecurity. Think of honeypots as traps set to catch hackers. It can be as simple as a website or as complex as an entire computer network. It is set up for the sole purpose of attracting a hacker to attack it.
This is done so that information can be learned about how the real target could anticipate being attacked. It can identify the common methods of attack. It can also identify vulnerabilities and ways to improve the real target.
How it works
I would best describe it as a straw man argument as referred to in debating. When someone makes a straw man argument, they may appear to be attacking the core premise of another person’s argument, however, they are really attacking a separate idea. An example is if I say I don’t like it when it rains because stepping in puddles makes my shoes wet. A straw man argument would be to attack the quality of my shoes or to avoid puddles.
Honeypot Name Means
One reason for the name honeypot is because of the adage that you attract more bees with honey than vinegar. However, you can more accurately associate the name with the nature of wild bears stealing honey. Regardless of the direct source, the premise remains the same. The sweet honey is just something that would attract a target, such as a criminal. Overall it represents something they desire.
In terms of Tor, some people suggest the government created Tor as a honeypot. The reason is there’s arguably a large amount of criminal activity associated with Tor because of its promised high security and privacy.
Because criminals can be attracted to a place where crimes can be committed without detection, the government could potentially use this as a trap. If this were true, Tor would obviously not be private. The information communicated by criminals through Tor would be intercepted by the government.
There are some similarities between a honey pot and another cybersecurity term. One example that comes to mind is phishing. This is another example of deception for the purpose of gathering information. Phishing can be one example of a honeypot. But honeypot is a broader term and includes any bait and switch data collection.
For example, someone downloads software thinking it does one thing when it’s really malware that collects data or allows remote access to files.
What is Tor?
Tor is a system of transmitting information over the internet anonymously. This can include privately browsing websites or sending and receiving messages and emails. Without Tor, this information has the potential for being intercepted and recognized. For example, a hacker or the government would be able to see where you are located or what your internet activity is. Tor provides the opportunity to remain private.
Tor stands for The Onion Routing project. Because Tor works by sending data through multiple relays, each layer is like the layers of an onion. In order to find the data sent, you would have to peel back each layer of the onion to find what’s inside.
The Tor process chooses each of these points in between at random and they encrypt the information before sending it. So, it is unlikely that someone can find your information, associate it with you, and decipher the meaning of the data.
As the title suggests, we have another article called Is Tor Safe for Normal Browsing? that explains the security of using Tor to visit regular mainstream websites. It also provides information on Tor and how it works in greater detail.
Tor Conspiracy Theories
The Claims
Before we get into the different theories, I want to first talk about the source of all the conspiracies. What I mean by that, is why there are conspiracies, to begin with. And I think that the number one factor is the source of Tor in general. It’s no secret that the government created Tor. So, it’s not hard to understand why some people think that the government has full control over this system.
Beyond that, what I’ve seen as the source of most conspiracies relating to Tor, is fear. There is a fear that the government has its hands in everything. This particular source of conspiracies is hard to disprove but it does not make it true. Most people know someone that holds certain things to be true no matter the evidence.
I am not trying to prove or disprove anything in this article. I hope that you find what follows to be more informative, and less argumentative.
Claim #1 – CIA/FBI Honeypot for Data Collection or Enforcement
The first claim is obviously that the federal government in the form of the CIA or the FBI uses Tor to collect information on people who think Tor is otherwise private. The reasoning is they can use this information for criminal prosecution. My general opinion about this viewpoint is that law enforcement is typically more reactive than it is proactive.
Meaning, someone commits a crime, it comes to the attention of law enforcement, and then they act. So, to say that they spy just to find criminals would appear that they are doing more than what is expected of them. However, to give this theory some credence, after the terrorist attacks on 9/11, law enforcement did shift to a more offensive rather than defensive approach.
Claim #2 – CIA/FBI Propaganda
The next belief is that rather than gathering information, the government is in fact disseminating it. This is the kind of activity that you would normally associate with countries such as China and North Korea.
However, it would be foolish to think that the United States does not participate in this activity to some degree. To what that degree is, is the unknown. What is uncertain, is if Tor is one of these avenues. In my opinion, there are other avenues that are more likely such as the media and entertainment industries through movies and music.
Claim #3 – Foreign Data Collection or Propaganda
Lastly, another theory would fall more along the lines of an outside actor. Rather than the source being spying from the FBI, this would fall along the same lines but involve another country. It should be no secret that countries such as China and Russia have a large presence of hackers. But it would also appear along with their ability, they do have a focus on the United States.
In my opinion, I think that an outside actor theory would be less likely because of the previously mentioned heavy involvement of the United States government. There are just some things that cannot be fully known unless you are a part of these agencies or countries.
Honeypot Examples
The following are cases of the government using honeypots. They are declassified and give a good insight into how the FBI uses honey traps.
Operation Torpedo
In 2011, the FBI began what was known as Operation Torpedo. This was a targeted attack that started with the taking of control over a server. This was no ordinary server. This particular one was responsible for running PedoBook. Pedo is a term commonly used as short for pedophilia. So it should be no surprise this site was for the purpose of hosting and disseminating child pornography.
To accomplish the task of taking over the server, the FBI had to secure a search warrant to conduct their investigation. Once obtained, the FBI developed software code in the form of malware to collect IP addresses. This identifies and differentiates each computer from the other. As a result, the person using the computer and accessing the server can be determined.
A vulnerability in Adobe’s Flash software was the vehicle used to deliver the malware. At one point, Flash was the primary software used when viewing websites. Weaknesses in its security helped lead to its decline and are what allowed the FBI honeypot to be successful in its mission.
Operation Pacifier
In 2015, another FBI mission took place. This one is called Operation Pacifier. It targeted PlayPen, a single website also used for illegal pictures. It was taken over by the FBI and used to collect IP addresses that connected to it. You can read more on the FBI’s website detailing Operation Pacifier.
Freedom Hosting Honeypot
Lastly, Freedom Hosting was infiltrated in 2013. This was an entire server dedicated to running multiple websites through Tor. Of the three operations mentioned, this was the biggest because it involved a whole network of websites. The server ran about 95% of sites depicting abuse of minors on Tor.
As in Operation Torpedo, the FBI in this operation took control of the server and used it to spread malware. The malware sent information without encryption to the FBI so they could use it to identify people accessing the sites. This operation targeted a vulnerability in an outdated version of the Firefox browser.
Key Takeaways
Considering the three examples above and the unknown number of other clandestine FBI operations, it is easy to be wary of Tor. However, Tor does not appear to be the target of the FBI. Obviously, not every site and not every user has involvement in illegal activity.
The FBI was required to obtain warrants that were later made publicly available in order to conduct these operations. They would not be able to obtain a warrant without probable cause of a crime. Therefore, it would not be legal to surveil Tor in its entirety.
Even so, conspiracies continue as they persist on the FBI or other government agencies not acting within the scope of the law. While this can be true, it would make it nearly impossible for successful prosecution in court – which after all is their ultimate endgame. Furthermore, if they can’t use the information they collect in court, they would not have a motive to collect it. Finally, they would not be interested in investigating activity that is legal.
In fact, all the above networks mentioned have the same thing in common. They are used for illegal pictures of children. Other examples of sites targeted are for illegal drug sales at a large scale such as the Silk Road. It is their criminal behavior that brings the attention of the FBI. Since Tor is not dedicated to illegal activity, its complete takeover as an FBI honeypot is unlikely.
How to avoid honeypots
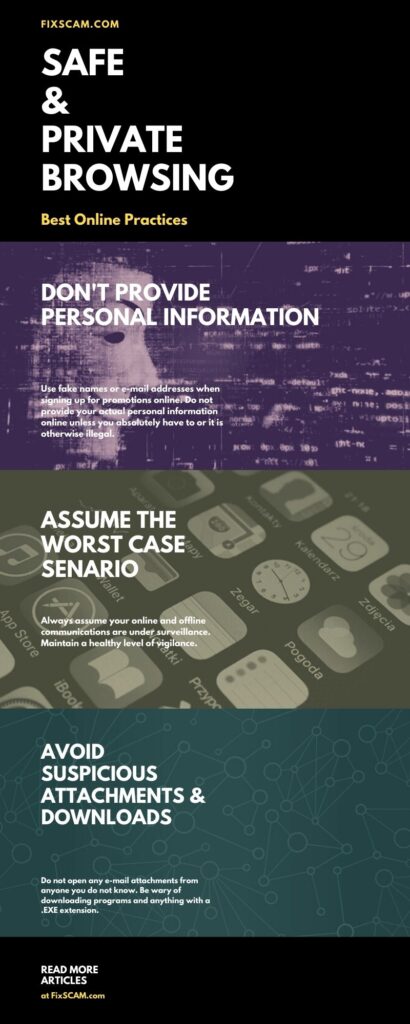
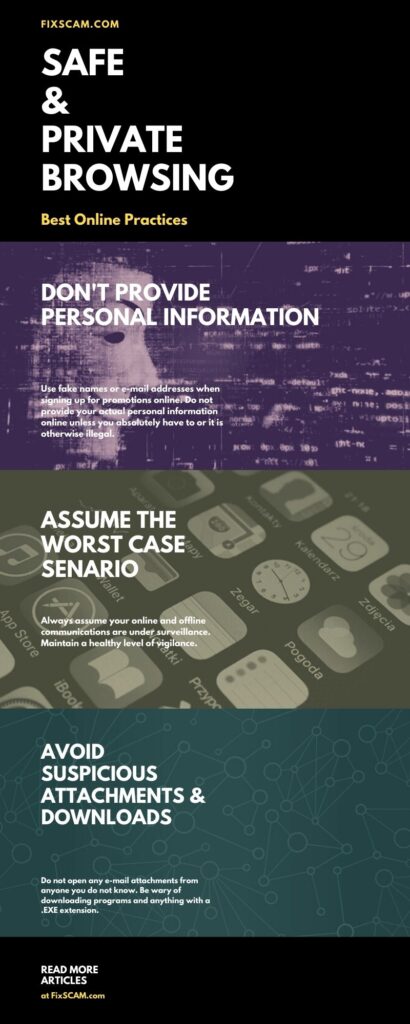
The best way to avoid one is to learn how to spot a honey trap. Security should be on the radar of everyone whose interest is in private and secure browsing.
- Update software
The FBI targets vulnerabilities in outdated software. See the above examples about Adobe Flash and Mozilla Firefox.
- Validate the source
Check links for misspellings, extra characters, or the wrong extension. For example, you might expect a dot com when instead it is a dot co.
- Check the connection
Is it Https? Is the certificate from a legitimate SSL site or is it a self-certification? If it is an e-commerce store or otherwise collects sensitive information such as credit card numbers, check the connection.
- Avoid software downloads and .EXE extensions
Be wary especially of unknown sources that try to get you to download something in an unexpected file format. They might say it’s a document but instead, it is an .EXE file
- What’s the offer? Is it too good to be true?
Are you trying to download for free something that should cost money? Is it a brand new, much sought-after, program or movie/tv show that usually isn’t available?
Fine-Tuned Suspicion
It’s normal to be suspicious of Tor. Many people, both users of the Tor browser, and hosts of Tor websites use it for criminal activity. Reactivated sites after being dormant may have been taken over by feds. This is just a rule of thumb or good practice. An example is when people consider drug users to be suspicious immediately after a new arrest. This is due to the possibility they are not cooperating with the police and could help arrest others.
Search or ask the community if you are dealing with a source with which you are unfamiliar. The experience of others can be an invaluable tool. For example, if someone else has knowledge of the source, you can rely on the experience of others and hopefully learn from their mistakes. This basic concept of reputation can be highly successful in defending against falling victim to a honeypot.
Conclusion
No, Tor is not a Honeypot. There are some sites and vendors that set up phishing traps. Tor is filled with illegal activities which are largely unregulated. This creates a greater opportunity for identity theft than browsing the regular internet.
What I ask for people to keep in mind is that a reasonable level of scrutiny is always appropriate. I do not believe in or promote blind compliance. However, reasonableness is the standard. Sometimes in order to find this standard, you often must look outside of yourself. So, I recommend that you take an open mind and do not discredit the input of others.
Finally, there is a common belief that if there is nothing to hide there is no reason to be afraid. I for one believe that privacy is of the utmost importance. However, I recommend that you do not participate in any activity in private that you cannot bear to have public.
Read more articles on our Blog about avoiding scams and staying safe online.